“Patch Tuesday” is an unofficial term referring to the second Tuesday of each month, when vendors including Microsoft, Adobe, SAP and Google coordinate the release of vulnerabilities in (and patches for) their software products on a fixed cycle. Critical security updates are occasionally released outside of the normal Patch Tuesday cycle, but these are known as “out-of-band” releases.
In this blog post we’ll summarise the key Microsoft Security Updates for the month, but you can access the raw list in full directly at https://msrc.microsoft.com/update-guide/releaseNote/2024-Nov
Updates this month feature patches for critical vulnerabilities including Remote Code Execution (RCE) and Elevation of Privilege (EoP). A smaller than usual bundle of fixes this month, but it still includes two vulnerabilities that have been confirmed as being currently exploited as ‘0-Day’ vulnerabilities in the wild before Microsoft released patches.
In early November, FortiGuard also reported evidence for the active exploitation of a vulnerability in Microsoft SQL Server dating from 2019 (CVE-2019-1068). This was being used to distribute the ransomware known as ‘Malloc’. It serves as a timely reminder of how important it is to ensure that patches from Microsoft are applied as soon as practicable, since otherwise, these older vulnerabilities will continue to provide a source of targets for attackers.
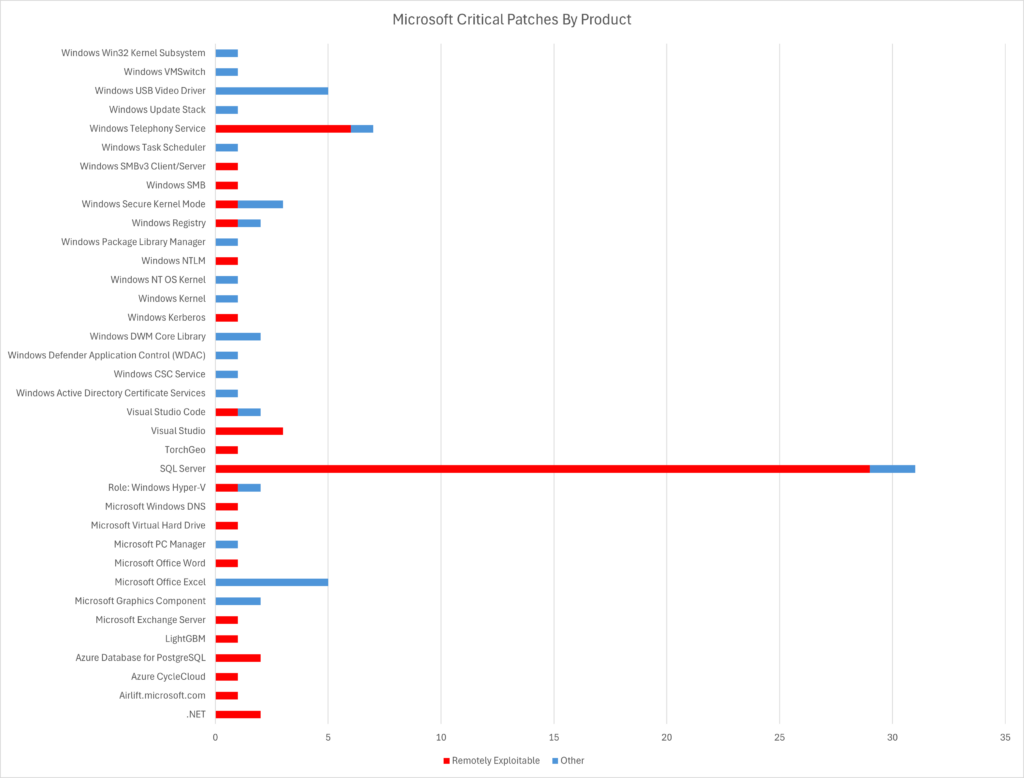
The Microsoft Patch Tuesday update for November 2024 also includes important updates for vulnerabilities in products including Microsoft Office, Microsoft SQL Server, .NET, Visual Studio, Azure CycleCloud, Azure Database for PostgreSQL, LightGBM and TorchGeo.
The list of “Known Exploited” vulnerabilities below represent the greatest risk and absolute highest priority for patching for many organisations. They have been reported by the CISA, America’s Cyber Defense Agency, to be known to be currently being exploited in the wild and at scale, meaning that not only is exploit code known to attackers, but that the weakness is being actively targeted. These vulnerabilities are the most time-critical to patch before being exploited by threat actors.
The AppCheck Scanner is able to detect these vulnerabilities and report on their presence in your technical estate, enabling you to effectively and swiftly target them for remediation – please click each CVE below to read more about each entry on our public-facing Detections database.
An NTLM hash disclosure vulnerability in Windows has been confirmed by Microsoft as undergoing active exploitation in the wild. Successful exploitation would allow attackers to leverage the disclosed NTLMv2 hashes in order to authenticate by posing as legitimate users, gaining access to any and all systems and services that user was authorised to access. There are few technical details available at the time of writing. However the vulnerability is reported to reside in the remaining tendrils spread throughout the operating system from the legacy Internet Explorer browser, which continues to deliver pain years after its formal retirement.
See more details in the AppCheck Detections Service at https://detections.appcheck-ng.com/vulnerabilities/view/330006
An elevation of privilege vulnerability in Task Scheduler is the second active exploitation now confirmed by Microsoft this month. Successful exploitation of this second critical flaw allows attackers to escalate their privileges and move from a low privileged environment to a higher privilege context. This means that the attacker could execute functions normally restricted to more privileged accounts. There are few technical details at this time but since the report is attributed to Google’s Threat Analysis Group (TAG) it is highly likely that the exploitation reported is being performed by a highly sophisticated advanced persistent threat (APT) or nation-state group – patching this one is critical now that MS has released a fix.
See more details in the AppCheck Detections Service at https://detections.appcheck-ng.com/vulnerabilities/view/330070
The list of “Critical” vulnerabilities below are all those with a “CVSS” (Common Vulnerability Scoring System) score of 9.0 or greater. This generally reflects a vulnerability that is a critical risk – being both trivial to exploit as well as having the potential to have significant impact (harm) if successfully exploited – but for which no hard evidence has been gathered yet as to ongoing exploitation. Critical vulnerabilities are crucial to patch, but may be slightly less time-sensitive than ‘known exploited’ vulnerabilities. Critical vulnerabilities highlighted by Microsoft this month include:
| Product | CVE | CVSS Score |
|---|---|---|
| Azure CycleCloud – Remote Code Execution (RCE) Vulnerability | CVE-2024-43602 | 9.9 |
| .NET and Visual Studio – Remote Code Execution (RCE) Vulnerability | CVE-2024-43498 | 9.8 |
| Windows Kerberos – Remote Code Execution (RCE) Vulnerability | CVE-2024-43639 | 9.8 |
| Windows Kernel – Elevation of Privilege (EoP) Vulnerability | CVE-2024-43640 | 9.8 |
The list of “Highly Exploitable” vulnerabilities below are all those which Microsoft has determined are relatively trivial to exploit. Unlike the ‘known exploited vulnerabilities’ list above, there is no evidence yet released of these vulnerabilities having been exploited ‘in the wild’, but that could well change if exploit code is published, or a threat actor chooses to specifically target one of these vulnerabilities. The vulnerabilities flagged as ‘highly exploitable’ by Microsoft this month include:
| Product | CVE | CVSS Score |
|---|---|---|
| Windows NT OS Kernel – Elevation of Privilege (EoP) Vulnerability | CVE-2024-43623 | 7.8 |
| Windows DWM Core Library – Elevation of Privilege (EoP) Vulnerability | CVE-2024-43629 | 7.8 |
| Windows Kernel – Elevation of Privilege (EoP) Vulnerability | CVE-2024-43630 | 7.8 |
| Win32k – Elevation of Privilege (EoP) Vulnerability | CVE-2024-43636 | [[CVSS SCORE]] |
| Windows SMB – Denial of Service (DoS) Vulnerability | CVE-2024-43642 | 7.5 |
| Active Directory Certificate Services – Elevation of Privilege (EoP) Vulnerability | CVE-2024-49019 | 7.8 |
| Microsoft Word – Security Feature Bypass Vulnerability | CVE-2024-49033 | 7.5 |
| Microsoft Exchange Server – Spoofing Vulnerability | CVE-2024-49040 | 7.5 |
In addition to the above, Microsoft released 89 important security patches in total.
Products affected by this Patch Tuesday’s updates include:
Total Microsoft CVEs: 89
Known Actively Exploited: 2
Critical: 4
Highly Exploitable: 8
Other vendors releasing critical security updates this Patch Tuesday include:
As with every month, if you don’t want to wait for your system to download Microsoft critical updates on pre-determined schedule, you can download them immediately from the Windows Update Catalog website at https://www.catalog.update.microsoft.com/Home.aspx and searching by Microsoft KB ID.
We also recommend scanning your entire estate using the AppCheck vulnerability scanner regularly – including end-user machines running desktop operating systems. Contact your account manager now if you are not already licensed for internal scan hubs to cover your whole estate.
The next MICROSOFT Patch Tuesday update will be on 10th December 2024 – add it to your calendar now!
We also now provide coverage of other critical vulnerability updates from key vendors, including:
AppCheck is a software security vendor based in the UK, offering a leading security scanning platform that automates the discovery of security flaws within organisations websites, applications, network, and cloud infrastructure. AppCheck are authorized by the Common Vulnerabilities and Exposures (CVE) Program as a CVE Numbering Authority (CNA).
No software to download or install.
Contact us or call us 0113 887 8380
AppCheck is a software security vendor based in the UK, offering a leading security scanning platform that automates the discovery of security flaws within organisations websites, applications, network and cloud infrastructure. AppCheck are authorised by the Common Vulnerabilities and Exposures (CVE) Program as a CVE Numbering Authority (CNA)







